Let’s talk about passwords
I had in mind an article about passwords but never got to write it down. However, since some dude posted on reddit a link to some info he received from his bank about password security I decided that I should start writing on the subject.
Now, first things first. According to the info provided by the bank referenced above, the key takeaway for stronger passwords in 2018 is that length and unpredictability are more important than wacky characters and other rules. And I could not agree more.
The bank provides four rules to follow when choosing a password in 2018 and based on those rules it seems that some of my passwords are no longer secure enough for 2018:
An unexpected four-word phrase—“SampleReductionEastPronounce”—is actually tougher to crack than any random 8-character password. Just don’t use “ILiveinMadison” or “MyDogsNameIsLulu.”
Add special characters and capital letters, but don’t put them at the beginning or end. And avoid !, by far the most common special character. If you use a four-word phrase, put special characters between words instead of spaces:
Slide>Marigold>Rice>Easy.Check your password’s strength at the Carnegie Mellon password meter, which analyzes your password against millions of known passwords and offers suggestions for making yours better.
Lie on security questions. Those personal details—mother’s maiden name, etc.—are frequently required when you reset a lost password. But the answers are often easy for anyone with access to your social media accounts to figure out. Make up fake answers you can remember or store somewhere secure. source
Now, that looks pretty straight forward right? Of course it does, but at the time of choosing such passwords it is either too complicated to come up with a perfect password that follows the rules and it’s also easy to remember.
So at the end of the day, the use of a password manager is probably the best choice, especially for those with way too many passwords to remember.
But there’s more to this subject than just some common sense recommendations made by a bank.
Let me start by saying that people use weak passwords because they are allowed to. Yup, you read that right.
The problem is not with the user, it’s with the system. I recently came across an organization that was using two letter passwords for some of their panels. That’s two fucking letters! Easy to guess, easier to bruteforce.
So who’s to blame? Well both the developer and sysadmin are to blame.
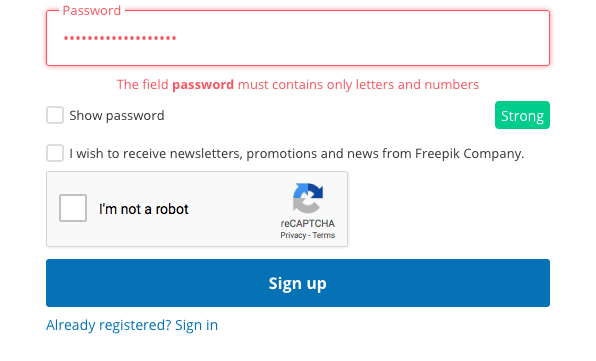
As a developer you can’t possibly code something that allows the use of weak passwords in 2018. You weren’t supposed to be doing it alt least since the early 2000’s so why still do it now.
Each year we see a list of the most common passwords used and we hear about major data leaks that made it possible for various password hashes to be cracked but we never see anyone pointing the finger at the developers that made this possible.
If every single developer would have a little common sense and responsibility sense and would implement specific requirements for the passwords then we would not see such lists, or at least we would not see such high numbers related to weak passwords.
The other guy responsible for the large volume of weak passwords used in the wild is the sysadmin. I mean seriously, setting higher password requirements for the internal network and external services that support this should be the sysadmin’s top priority and he should be doing this before installing the antivirus on the user’s PC.
The user that gets hacked, although blamed by everyone and held responsible for using weak passwords is in the end just a victim which used weak passwords because nobody told him that’s unsafe and nobody requested that he used more secure ones.

